Critical Infrastructure Security: Where to Start
Critical infrastructure security does not begin with buying more cameras, adding more guards, or layering on another software platform. It starts with a disciplined understanding of what must stay operational, what could fail, who might exploit it, and how physical, cyber, operational, and governance controls work together. For operators, project leaders, and enterprise decision-makers, the fastest way to make progress is to define critical assets, rank operational consequences, align with applicable security standards, and build an integration roadmap that is realistic for the site, budget, and regulatory environment.
Whether the environment is a utility, transport hub, manufacturing campus, data center, smart building portfolio, or urban infrastructure project, the challenge is usually the same: too many disconnected systems, too little risk prioritization, and unclear ownership between security, IT, operations, engineering, and compliance teams. This guide explains where to start, what to assess first, and how to move from fragmented protection to resilient, compliant, future-ready infrastructure security.
Start with one question: what failure would hurt operations the most?
The core search intent behind “Critical Infrastructure Security: Where to Start” is practical, not theoretical. Most readers are not looking for a broad definition of critical infrastructure security. They want a starting framework they can apply: what to assess first, which risks matter most, how to prioritize investments, and how to avoid building a security program that looks complete on paper but fails under real conditions.
That is why the right starting point is not technology selection. It is consequence mapping. Before discussing Industrial Security, Urban Security, Physical Security, Digital Twin deployment, or Data Governance, teams need a clear answer to these questions:
- Which assets are truly mission-critical?
- What would happen if they were disrupted, manipulated, accessed, or damaged?
- Would the consequence be safety-related, operational, financial, environmental, regulatory, or reputational?
- How quickly would the impact spread across other systems, facilities, or public services?
For example, a perimeter breach at a logistics yard and a compromise of a substation control area are both security events, but they do not have the same consequence profile. Critical infrastructure security begins by distinguishing nuisance events from high-impact disruptions. Without that distinction, organizations often overspend on visible controls while under-protecting essential processes.
What most decision-makers and operators care about first
Across enterprise leadership, project teams, operators, and quality or safety managers, the most common concerns are highly practical:
- Where do we begin without wasting budget?
- Which standards and compliance obligations apply to our environment?
- How do we connect surveillance, access control, sensors, and building systems without creating new vulnerabilities?
- How do we justify investments to management or procurement?
- How do we reduce operational risk while keeping systems usable for frontline teams?
- How do we prepare for future scale, audits, and incident response?
These concerns point to a useful principle: the value of a security program is not measured by device count. It is measured by reduction in operational uncertainty. A strong infrastructure security strategy helps teams detect earlier, verify faster, respond more accurately, document decisions better, and maintain compliance without slowing the business.
Begin with a structured baseline assessment, not a product shortlist
If you are asking where to start, the first actionable step is a baseline assessment across five domains:
- Asset criticality — Identify facilities, zones, systems, and processes whose failure would materially affect operations or public safety.
- Threat exposure — Review relevant risks such as intrusion, sabotage, theft, insider threats, terrorism, vandalism, environmental conditions, and coordinated physical-cyber incidents.
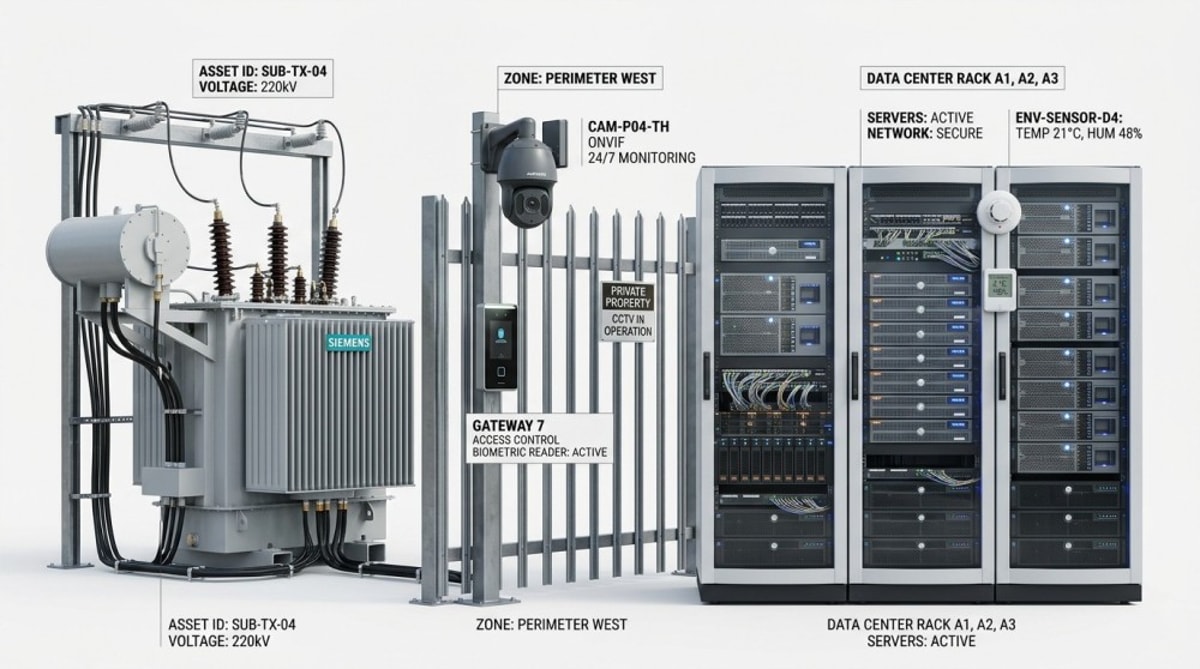
- Current control maturity — Evaluate what is already deployed: video surveillance, perimeter protection, access control, biometrics, building management systems, thermal imaging, alarm workflows, and staffing protocols.
- Integration quality — Determine whether systems operate in silos or support correlated detection, alerting, identity validation, event logging, and response escalation.
- Governance and compliance — Check whether data retention, privacy, access permissions, procurement standards, and audit trails are defined and enforced.
This assessment should produce a gap map, not just a list of devices. For instance, a site may already have strong camera coverage but weak credential governance; good access control hardware but no anti-tailgating workflow; thermal detection for perimeter monitoring but no verified escalation path into the command center. In critical infrastructure, weak process integration often creates more risk than missing hardware.
Prioritize physical security, but do it in the context of operations
Physical Security is still the foundation for many critical environments, especially where human access, equipment protection, and perimeter integrity are central. But the best-performing programs design physical security around operational realities.
That means asking:
- Which zones require deterrence, detection, delay, and response?
- Where are the real choke points for people, vehicles, contractors, and maintenance teams?
- Which assets must remain accessible for operations but protected against unauthorized handling?
- Which environments have poor visibility, long perimeter lines, or low-light conditions that make conventional monitoring insufficient?
In many sectors, this leads to a layered architecture that may include:
- Perimeter intrusion detection
- AI-enabled video surveillance for event classification
- Smart Access Control and Biometrics for restricted zones
- Thermal Imaging and Infrared Sensing for long-range or low-visibility monitoring
- Integrated alarm and incident workflows
- Hardened control rooms and secure equipment enclosures
The point is not to deploy every available technology. It is to match controls to real risk conditions. A remote energy site, a city transit interchange, and a pharmaceutical manufacturing facility all have different exposure patterns and response requirements.
Industrial security and urban security need different starting models
One reason infrastructure programs stall is that organizations use generic security templates for very different environments. Industrial Security and Urban Security overlap, but they are not identical.
Industrial Security usually demands emphasis on operational continuity, restricted process zones, equipment protection, contractor management, and the consequences of process interruption. Here, teams should focus early on:
- Critical process areas and control rooms
- Maintenance access and temporary permissions
- Environmental resilience of sensors and devices
- Integration with plant or facility operations
- Tamper visibility and chain-of-custody records
Urban Security often requires more attention to public access, high traffic variability, distributed assets, privacy regulation, multi-agency coordination, and rapid situational awareness. In smart city contexts, priorities often include:
- Public-space monitoring with legal and privacy controls
- Transport node protection
- Incident verification across multiple locations
- Real-time visibility for city operations centers
- Interoperability between departments and vendors
Understanding which model better reflects your environment helps determine the right starting scope, acceptable response times, and technology mix.
Security standards matter early, not just before procurement
Another major reader concern is standards. Many teams delay security standards review until procurement or audit preparation, which is too late. Standards should inform architecture decisions from the beginning, especially when projects involve public tenders, cross-border operations, regulated industries, or long-life infrastructure assets.
Relevant standards and frameworks will vary, but organizations commonly need to consider areas such as:
- Product safety and performance certifications
- Video and device interoperability standards such as ONVIF
- Electrical and installation compliance
- Cybersecurity hardening requirements for connected devices
- Privacy and data governance obligations, including GDPR-related principles where applicable
- Procurement restrictions, supply chain screening, and NDAA-related requirements in some markets
- Industry-specific operational and safety regulations
For decision-makers, the practical takeaway is simple: standards reduce future friction. They improve interoperability, support audit readiness, lower vendor lock-in risk, and make system expansion more manageable. For project leaders, standards also create a more defensible basis for technical specifications and vendor evaluation.
System integration is where infrastructure security either succeeds or breaks down
Many organizations already own capable hardware. Their real weakness is fragmented architecture. Cameras do not talk meaningfully to access control. Access events are not correlated with alarms. Building systems generate alerts that security teams do not see in context. Incident logs are incomplete. Operators switch between too many interfaces.
This is why integration should be treated as a security control, not an IT afterthought.
A useful integration roadmap should clarify:
- Which systems must exchange events in real time
- Which alerts require automated escalation
- How identity, video, environmental sensing, and facility status are correlated
- Where command-and-control visibility is centralized
- How third-party devices are validated and governed
In advanced environments, Intelligent Building Management Systems, AI vision platforms, access control, and thermal sensing can be linked into a common operational picture. When well designed, this improves situational awareness, reduces false positives, and shortens response times. When poorly designed, it creates complexity, data overload, and maintenance headaches. The difference usually comes down to architecture discipline and governance.
Digital Twin deployment is valuable only if it supports real decisions
Digital Twin strategies are increasingly discussed in critical infrastructure, but many teams still question where they fit. The answer is that Digital Twin deployment is most useful when it improves visibility across asset relationships, site conditions, and incident response planning.
A Digital Twin can help teams:
- Visualize critical zones, dependencies, and blind spots
- Simulate incident scenarios and response paths
- Coordinate maintenance, upgrades, and security changes
- Improve cross-functional planning between engineering, operations, and security
- Support lifecycle decision-making for large or distributed sites
However, a Digital Twin is not a starting point if the organization has not yet completed basic asset classification, integration cleanup, and governance design. In other words, do not use a Digital Twin to compensate for missing fundamentals. Use it to enhance a security architecture that already has defined assets, connected systems, and clear ownership.
Data governance is now central to infrastructure security
As video, biometrics, analytics, access logs, and sensor data become more interconnected, Data Governance becomes a frontline security issue. This is especially important in Smart City deployments, enterprise campuses, transport infrastructure, and any environment combining AI-enabled monitoring with regulated personal or operational data.
Strong data governance should answer:
- What data is collected, and why?
- Who can access live feeds, identity records, analytics outputs, and audit logs?
- How long is data retained?
- Where is it stored and processed?
- How are integrity, privacy, and chain-of-custody maintained?
- How are vendors, integrators, and service providers controlled?
For enterprise decision-makers, this is not just a compliance exercise. Poor data governance can create legal exposure, procurement delays, public trust issues, and operational confusion during incidents. Good governance, by contrast, gives teams confidence that security data is reliable, defensible, and usable.
How to evaluate sensor and surveillance investments more intelligently
In critical infrastructure projects, buyers often compare devices based on top-line specifications alone. That approach is risky. Sensor Manufacturing quality, environmental fit, and integration maturity matter as much as raw performance claims.
When assessing video surveillance, thermal imaging, biometrics, or related sensing systems, ask:
- Will this perform reliably in our real lighting, weather, vibration, distance, and maintenance conditions?
- Does it meet required interoperability and certification standards?
- Can it be managed securely over its lifecycle?
- Will operators trust and use the outputs?
- How does it affect false alarm rates, staffing workload, and incident verification time?
For example, Infrared Sensing may be far more effective than standard visible-light surveillance in low-visibility perimeter conditions. AI-driven cameras may improve detection efficiency, but only if the analytics are tuned to site behavior and operational tolerances. Biometrics may strengthen restricted access, but only when privacy, fallback access, and user enrollment quality are properly managed.
The best investment decisions are made at the system level, not the device level.
A practical first-90-days roadmap
For organizations looking for an actionable starting sequence, this is a realistic first-90-days approach:
- Define the critical asset list — Identify the systems, areas, and services that cannot fail without major consequence.
- Map top threat scenarios — Focus on credible threats, not every possible risk.
- Assess existing controls — Review physical, procedural, and digital controls already in place.
- Find integration gaps — Document where systems are isolated, duplicated, or operationally weak.
- Review standards and regulatory requirements — Include procurement, privacy, interoperability, and relevant sector rules.
- Rank quick wins vs. structural upgrades — Separate immediate risk reduction from long-term architecture projects.
- Assign ownership — Clarify who owns security design, operations, data governance, maintenance, and incident response.
- Build a phased investment plan — Tie spend to risk reduction, operational value, and compliance needs.
This phased approach helps avoid a common failure pattern: launching large security transformation projects before the organization has agreed on priorities, responsibilities, and decision criteria.
Conclusion: the right place to start is clarity, not complexity
Critical infrastructure security starts with clarity about consequences, assets, risks, standards, and integration needs. For most organizations, the biggest early win is not adding more tools. It is creating a shared operational picture of what must be protected, how current controls perform, and where governance or system design gaps create the greatest exposure.
If you are evaluating where to start, focus first on criticality, consequence, control maturity, and interoperability. Then align Physical Security, Industrial Security, Urban Security, Digital Twin planning, and Data Governance around those priorities. That is how infrastructure security becomes not just stronger, but more measurable, more compliant, and more useful to the people responsible for keeping essential services running.
Related News
Thermal Sensing
Curation by industry experts
Popular Tags
Related Industries
- Wireless IP Camera Wholesale: What Affects Range, Stability, and Return RatesWireless IP camera wholesale: learn what really affects range, signal stability, and return rates so buyers can reduce sourcing risk, lower costs, and choose more reliable deployments.
- Underwater Security Camera OEM Requirements That Are Easy to MissUnderwater security camera OEM requirements often fail in hidden details like pressure tolerance, sealing, transmission, and maintenance. Learn what to check before sourcing.
- When a Panoramic Camera Factory Is the Better Fit Than Multi-Camera CoveragePanoramic camera factory solutions can outperform multi-camera coverage in open B2B spaces by reducing complexity, improving scene continuity, and supporting smarter, scalable security design.
Weekly Insights
Stay ahead with our curated technology reports delivered every Monday.
