Industrial Security Gaps in HVAC IoT Systems
As HVAC IoT systems become integral to Smart City operations and Critical Infrastructure resilience, overlooked Industrial Security gaps can expose both Physical Security and Data Governance failures. From weak Security Standards to blind spots in Digital Twin integration, these risks affect operators, project leaders, and enterprise decision-makers alike. Understanding how Sensor Manufacturing, Urban Security demands, and even Infrared Sensing intersect is now essential for safer, more intelligent buildings.
For operators, the issue is no longer limited to temperature control, airflow optimization, or energy efficiency. Once HVAC platforms are connected to enterprise networks, cloud dashboards, occupancy analytics, and integrated building management systems, they become part of the wider industrial attack surface. A compromised air-handling unit, smart chiller controller, or BACnet gateway can disrupt operational continuity in hospitals, airports, data centers, logistics campuses, and government buildings within minutes.
For procurement leaders and security managers, the challenge is more complex: many HVAC IoT deployments still inherit fragmented device inventories, uneven firmware maintenance, weak credential policies, and poor segmentation between OT and IT layers. In critical infrastructure settings, even a 2-hour HVAC outage can affect compliance, occupant safety, and asset protection. The right response requires a disciplined view of system architecture, lifecycle risk, and vendor accountability.
Why HVAC IoT Has Become a High-Value Industrial Security Target
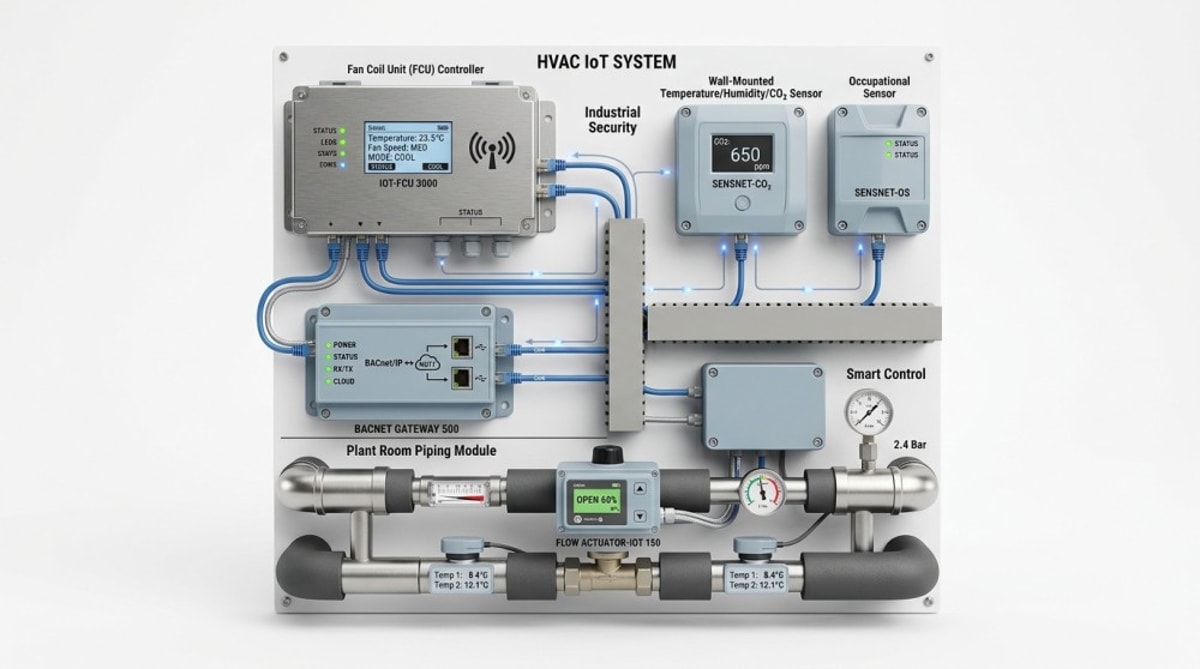
HVAC systems were once seen as operational utilities. Today, they are intelligent endpoints connected to sensors, controllers, edge gateways, cloud platforms, and facility dashboards. In a large commercial or industrial site, a single building may include 50 to 500 connected HVAC assets, each generating telemetry every 5 seconds to 15 minutes. That density creates visibility benefits, but it also creates multiple access paths for intrusion, manipulation, and lateral movement.
Attackers target HVAC IoT for three practical reasons. First, many devices run long lifecycle equipment, often 8 to 15 years, with outdated firmware and limited patch discipline. Second, building systems are frequently bridged to enterprise networks for remote maintenance, creating weak points between OT and IT. Third, environmental systems influence business continuity directly: overheating in a server room, incorrect pressure control in a cleanroom, or ventilation failure in a transport hub can escalate into a safety event quickly.
In smart city and critical infrastructure environments, HVAC data is no longer isolated engineering data. It may be linked to occupancy behavior, access control schedules, camera analytics, and digital twin models. This means an HVAC compromise can affect both physical operations and data governance obligations. If a vendor cloud account, mobile maintenance app, or exposed API is poorly secured, the issue moves beyond maintenance risk into enterprise security risk.
Common exposure points in real deployments
The most frequent gaps are not advanced zero-day threats. They are basic architectural weaknesses that accumulate over time. In many facilities, project teams inherit mixed-vendor systems added in 3 to 6 upgrade phases, with limited governance over password rotation, protocol hardening, or remote access control. As a result, security posture becomes inconsistent across sites and portfolios.
- Default or shared credentials on controllers, gateways, and engineering workstations.
- Flat network design with insufficient separation between HVAC OT, CCTV, access control, and enterprise IT.
- Unpatched firmware on field devices for 12 to 36 months after deployment.
- Insecure legacy protocols or weak protocol configuration in BACnet, Modbus, or proprietary device interfaces.
- Third-party remote maintenance sessions without multi-factor authentication or session logging.
These gaps matter because HVAC platforms rarely fail alone. They interact with elevators, smoke control, occupancy systems, lighting, and emergency procedures. A malicious setpoint change of just 3°C to 5°C may seem minor, but in regulated environments it can trigger inventory loss, workflow interruption, or compliance investigation.
The Most Critical Security Gaps in Connected HVAC Architecture
Industrial security gaps in HVAC IoT generally appear across four layers: device, network, platform, and governance. Each layer requires different controls, and many organizations over-focus on perimeter protection while neglecting configuration integrity and operational process. A robust assessment should map at least 20 to 40 control points across these layers before new procurement or retrofit decisions are made.
Device-level weaknesses
Field devices such as thermostats, variable air volume controllers, actuators, and edge sensors are often selected for performance, price, and protocol compatibility, but not always for secure lifecycle management. Secure boot, firmware signing, tamper logging, and certificate-based authentication remain uneven across product categories. When sensor manufacturing quality is strong but device security architecture is weak, the result is a high-performance but low-trust environment.
Network and protocol risks
Many facilities still rely on operational convenience rather than segmented design. If HVAC gateways share the same switching domain as workstation traffic or if remote vendor access bypasses a secure jump host, attackers can move more easily between systems. The issue becomes more severe where one building uses 2 to 4 protocol bridges to connect legacy plant equipment with a cloud analytics platform.
The table below highlights typical security gaps and their operational effect in integrated building environments.
The key conclusion is that cybersecurity and operational reliability are inseparable in HVAC IoT. Controls should be prioritized not only by technical severity but also by consequence: occupant safety, downtime cost, environmental compliance, and recovery time. In many projects, a 4-step hardening program delivers more value than adding another analytics layer on an insecure base.
Digital Twin, Space Intelligence, and the New Data Governance Problem
As building operators adopt digital twin platforms, the security conversation shifts from isolated devices to data-rich operational models. HVAC telemetry is increasingly fused with occupancy counts, access events, camera-derived movement patterns, indoor air quality, and maintenance workflows. This improves planning and space intelligence, but it also increases data sensitivity. A poorly governed integration can expose not only equipment status but also patterns of human presence and critical zone usage.
Digital twin blind spots usually emerge in middleware and integration logic. Teams may validate sensor accuracy within ±1°C or confirm dashboard latency under 30 seconds, yet fail to review API permissions, retention policies, cross-system identity mapping, and auditability. In a regulated enterprise, that gap can create legal and contractual issues, especially where privacy rules and procurement standards require traceable data handling.
Why data governance matters in physical environments
HVAC telemetry may appear harmless when viewed alone. However, when combined with access control, smart scheduling, people counting, or infrared sensing, it can reveal high-value operational patterns. Examples include executive area occupancy windows, loading dock activity cycles, lab usage density, or server room access timing. For critical infrastructure, such data can become operational intelligence if exposed externally.
The table below outlines how digital twin integration expands security and governance responsibilities for project teams.
A practical governance baseline should define 4 things from day one: who can see what data, how long data is retained, where data is stored, and how access is logged. For large multi-site portfolios, a quarterly review cycle is often more realistic than annual review, because integrations change quickly after commissioning.
How to Assess Vendors, Systems, and Procurement Readiness
For decision-makers, buying secure HVAC IoT is not only about selecting hardware. It requires evaluating lifecycle discipline, interoperability risk, remote service control, documentation quality, and the vendor’s ability to support secure operation over 5 to 10 years. A low upfront device cost can become expensive if commissioning, patching, or incident handling depends on undocumented tools or single-person vendor knowledge.
Five procurement questions that reduce downstream risk
- What is the supported firmware maintenance cycle, and how often are security updates issued over a 12-month period?
- Can the system support role-based access, multi-factor authentication, and session logging for internal and third-party users?
- Which standards and protocols are supported, and can insecure services be disabled during commissioning?
- How are device inventories, configuration backups, and change records maintained across multiple sites?
- What is the documented recovery plan if a controller, gateway, or cloud connection fails?
Procurement teams should also align building engineers, cybersecurity teams, and compliance stakeholders before final award. Many project failures occur because technical specifications focus on control logic and energy targets, while access management and data governance remain buried in generic IT clauses. In integrated environments, that separation is no longer effective.
Practical vendor evaluation matrix
The following matrix can help compare suppliers, integrators, and managed service partners during pre-qualification or final shortlist review.
The most reliable procurement outcome usually comes from a staged approach: 2 to 3 shortlisted vendors, a structured technical workshop, a hardening checklist review, and a pilot validation in one representative zone or building. That process reduces retrofit surprises and clarifies accountability before full deployment.
Implementation Roadmap for Safer HVAC IoT in Smart Buildings
A secure HVAC IoT program does not need to start with a complete system replacement. In most portfolios, the better path is phased risk reduction. This is particularly true for hospitals, campuses, industrial parks, and public-sector estates where uptime and budget constraints require staged modernization. A 90-day improvement cycle can address major weaknesses without disrupting core operations.
A practical 5-step roadmap
- Build a verified asset inventory covering controllers, gateways, software versions, network paths, and remote access methods.
- Segment HVAC OT from enterprise IT and adjacent smart building domains using role-based access and controlled communication paths.
- Harden devices by removing default credentials, disabling unused services, standardizing secure configurations, and backing up baseline settings.
- Define patch, monitoring, and incident-response routines with clear ownership across facilities, IT, and vendors.
- Review data governance for digital twin, occupancy, and thermal analytics integrations at least every 90 days.
Operators should also set clear thresholds for alarm handling and anomaly escalation. For example, repeated unauthorized setpoint changes within a 24-hour window, unexplained device reboots, or remote access outside approved maintenance hours should trigger review. Simple thresholds are often more effective than complex dashboards if teams are still building operational maturity.
Common implementation mistakes
- Treating building automation security as a one-time commissioning task rather than an ongoing operating discipline.
- Allowing third-party support access without time limits, approval workflow, or log retention.
- Integrating digital twin and analytics platforms before establishing asset identity, role governance, and retention rules.
- Assuming sensor accuracy and system efficiency automatically imply secure operation.
The strongest long-term result comes from convergence. Security managers, project leaders, building engineers, and procurement teams should review the same architecture map, risk register, and service obligations. When all four groups align on 6 to 10 critical controls, resilience improves faster than when each team optimizes its own silo.
FAQ for Operators, Project Leaders, and Enterprise Buyers
How often should HVAC IoT systems be reviewed for security?
A basic review every 6 to 12 months is common, but high-value sites such as data centers, transport facilities, healthcare campuses, and multi-tenant critical buildings benefit from quarterly review. Any major integration change, vendor access change, or firmware rollout should trigger an additional targeted assessment.
Which sites are most exposed to HVAC-related industrial security issues?
Sites with 3 characteristics carry higher exposure: high occupancy, high uptime dependency, and high integration density. This includes airports, hospitals, smart campuses, industrial cleanrooms, utilities, and buildings running integrated IBMS platforms with access control, surveillance, and digital twin overlays.
Is replacing old equipment always necessary?
No. Many organizations can reduce risk significantly through segmentation, credential control, secure gateways, improved logging, and better vendor-access governance. Replacement becomes more urgent when hardware cannot support secure configuration, patching, or reliable integration controls over the next 3 to 5 years.
What should procurement teams request from vendors before award?
At minimum, request an architecture diagram, firmware support policy, hardening guidance, remote access method, change-control workflow, backup and recovery process, and evidence of standards alignment where relevant. These documents are often more useful than marketing feature lists because they reveal operational maturity.
Industrial security gaps in HVAC IoT systems are rarely caused by one dramatic failure. More often, they arise from small omissions across design, integration, access control, maintenance, and governance. For smart buildings and critical infrastructure, those omissions can affect uptime, compliance, safety, and executive trust. A structured approach that combines secure architecture, disciplined procurement, and accountable lifecycle management gives operators and decision-makers a practical path forward.
G-SSI supports organizations that need a sharper view of integrated building risk, technical benchmarking, and security-oriented decision support across smart security and space intelligence domains. If you are evaluating HVAC IoT upgrades, digital twin integration, or secure IBMS procurement, contact us to obtain a tailored framework, compare solution paths, and explore the right next step for your facility portfolio.
Related News
Thermal Sensing
Curation by industry experts
Popular Tags
Related Industries
- Wireless IP Camera Wholesale: What Affects Range, Stability, and Return RatesWireless IP camera wholesale: learn what really affects range, signal stability, and return rates so buyers can reduce sourcing risk, lower costs, and choose more reliable deployments.
- Underwater Security Camera OEM Requirements That Are Easy to MissUnderwater security camera OEM requirements often fail in hidden details like pressure tolerance, sealing, transmission, and maintenance. Learn what to check before sourcing.
- When a Panoramic Camera Factory Is the Better Fit Than Multi-Camera CoveragePanoramic camera factory solutions can outperform multi-camera coverage in open B2B spaces by reducing complexity, improving scene continuity, and supporting smarter, scalable security design.
Weekly Insights
Stay ahead with our curated technology reports delivered every Monday.
